20 Easy Ideas For Picking Wallet Sites
Wiki Article
"The Zk-Powered Shield" How Zk-Snarks Hide Your Ip And Identity From The World
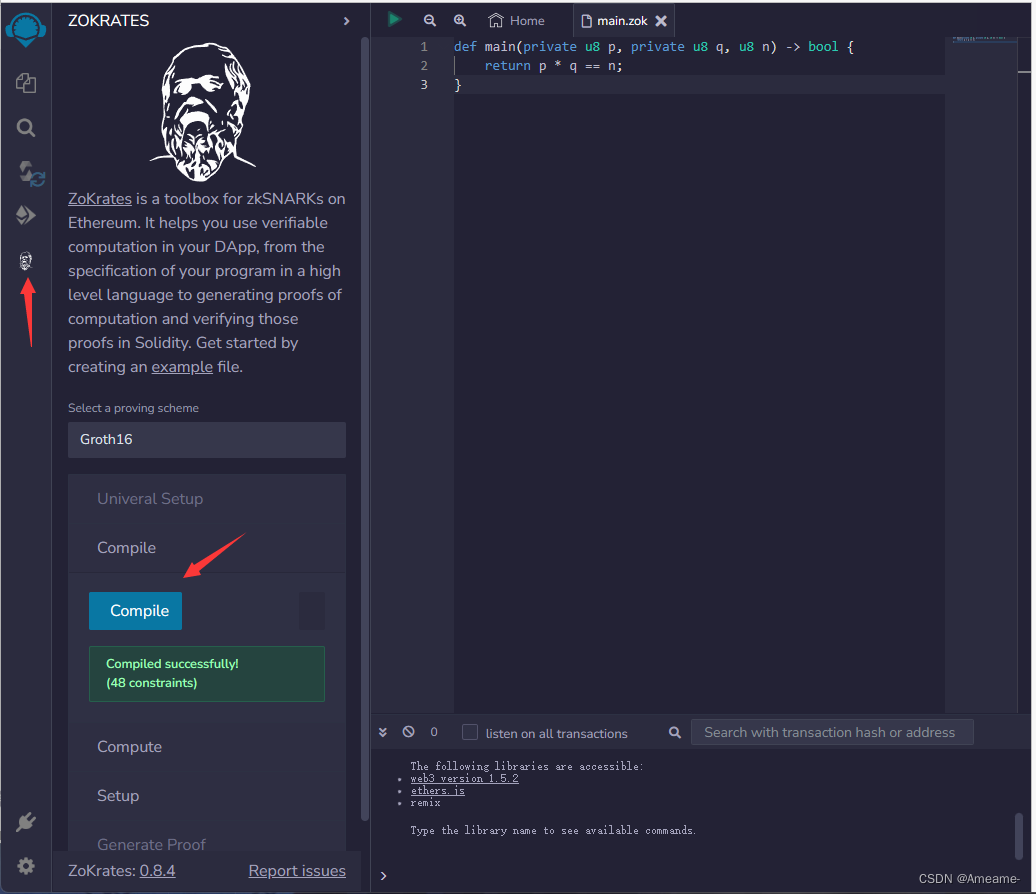
For many years, privacy instruments employ a strategy of "hiding in the crowd." VPNs funnel you through a server; Tor helps you bounce around the various nodes. They're effective, however they basically hide the origin by shifting it in a way that doesn't require divulging. Zk-SNARKs (Zero-Knowledge Succinct, Non-Interactive Arguments of Knowledge) introduce a completely different model: you must prove you're authorized to carry out an act and not reveal the authority the entity is. This is what Z-Text does. it is possible to broadcast your message on the BitcoinZ blockchain. The system can prove that you're an authentic participant using an active shielded identity, however, it's impossible to know which account sent it. Your address, your name along with your participation in the conversation becomes mathematically unknowable to the observer, yet in fact, it's valid and enforceable to the protocol.
1. A Dissolution for the Sender-Recipient Link
A traditional message, even if it's encryption, will reveal that the conversation is taking place. One observer notices "Alice communicates with Bob." zk-SNARKs completely break this link. When Z-Text broadcasts a shielded payment it confirms it is valid and that the sender has sufficient balance with the proper keys without divulging the sender's address or the recipient's address. To an observer outside the system, the transaction is viewed as encryption noise coming directly from the network, that is, not from a particular user. The relationship between two humans is now computationally impossible to identify.
2. IP Protecting IP addresses at the Protocol Level, and not the App Level
VPNs as well as Tor safeguard your IP because they route traffic through intermediaries, but those intermediaries will become a new source of trust. Z-Text's use for zk SARKs signifies the IP you use is not important in the verification process. As you broadcast your secured message on the BitcoinZ peer-to-peer network, it means you are part of a network of thousands nodes. This zk-proof guarantee that if an observer watches the transmissions on the network, they cannot connect the message received in the same way as the specific wallet has created it. The verification doesn't provide that data. The IP's information is irrelevant.
3. The Abrogation of the "Viewing Key" Challenge
In most blockchain privacy applications they have"viewing keys," or "viewing key" which can be used to decrypt transaction information. Zk's SNARKs in Zcash's Sapling protocol and Z-Text will allow for selective disclosure. You are able to demonstrate that you've communicated with them with no divulging your IP or the transactions you made, or even the full content of that message. The evidence is the only item shared. This level of detail isn't possible in IP-based systems as revealing this message will reveal the destination address.
4. Mathematical Anonymity Sets That Scale globally
When you are using a mixing or a VPN in a mixing service or a VPN, your anonymity is restricted to other users of that particular pool at that particular moment. If you are using zk's SNARKs for a VPN, the privacy secured is each shielded address within the BitcoinZ blockchain. Since the certificate proves it is indeed a secured address, one of which is potentially million, but does not provide any detail of the address, your privateness is scaled with the rest of the network. It isn't just the confines of a tiny group of friends and strangers, but rather in a vast crowd of cryptographic identities.
5. Resistance to Timing Analysis and Timing attacks
Expertly-crafted adversaries don't just scan IP addresses; they study the traffic patterns. They look at who sends data in what order, and also correlate timing. Z-Text's use, using zkSNARKs along with the blockchain mempool allows decoupling of operation from broadcast. You may create a valid proof offline and broadcast it later for a node to broadcast the proof. When you broadcast a proof, the time it was made for its presence in a bloc is not always correlated to the date you made it, abusing timing analysis, which typically can be used to defeat simpler tools for anonymity.
6. Quantum Resistance With Hidden Keys
IP addresses can't be considered quantum-resistant. In the event that an adversary could observe your activity and later break the encryption by linking them to you. Zk-SNARKs, which are used by Z-Text to secure your keys. Your public keys will not be disclosed on blockchains because your proof of identity confirms your key is valid without showing it. Any quantum computer, when it comes to the future would look only at the proof and not the key. Your previous communications are still private because the security key used verify them was never disclosed to the possibility of being cracked.
7. The unlinkable identity of multiple conversations
With a single wallet seed it is possible to generate several secured addresses. Zk-SNARKs allow you to prove to be the owner account without knowing the one you own. It means that you are able to have to have ten conversations with ten different individuals. No person, not even blockchain itself, can link those conversations to the specific wallet seed. The social graph of your network is mathematically dispersed by design.
8. elimination of Metadata as an attack surface
Security experts and regulators frequently say "we don't require the content or the metadata." The IP address is metadata. Anyone you connect with can be metadata. Zk-SNARKs stand out among privacy solutions because they disguise metadata at the cryptographic level. Transactions themselves are not populated with "from" or "to" fields that are plaintext. There's no metadata attached to make a subpoena. The only data is the evidence, and that is only what proves that an event occurred, and not the parties.
9. Trustless Broadcasting Through the P2P Network
In the event that you choose to use an VPN you are able to trust the VPN service to not keep track of. When you use Tor you can trust that the exit network not to watch you. Utilizing ZText, it broadcasts transactions that are zk-proofed to the BitcoinZ peer-to'-peer community. It connects to random nodes. You then transmit the details, then break off. Nodes are not learning anything, as the proof reveals nothing. They can't even know if you are the originator, in the event that you are transmitting for another. The network can become a reliable transmitter of private information.
10. "The Philosophical Leap: Privacy Without Obfuscation
Then, zk SNARKs make a leap of thought over "hiding" toward "proving by not divulging." Obfuscation techniques recognize that the truth (your IP, identity) is a threat and must be concealed. Zk-SNARKs believe that truth isn't important. It is only necessary for the protocol to know that you are registered. The change from reactive disguise and proactive relevance forms one of the fundamental components of the ZK shield. Identity and your IP aren't hidden. They have no relevance to the function of the network, therefore they're never required nor transmitted. They are also not exposed. Take a look at the top rated blockchain for blog info including encrypted text message, encrypted text, text privately, encrypted app, messages messaging, private message app, text messenger, encrypted text message, messages in messenger, encrypted message in messenger and more.
Quantum-Proofing Your Chats: Why Z-Addresses And Zk-Proofs Resist Future Encryption
Quantum computing tends to be discussed as an abstract concept, like a future boogeyman that will break all encryption. It is actually more specific and crucial. Shor's algorithm, when run on a strong quantum machine, could potentially break the elliptic-curve cryptography that secures most of the internet as well as blockchain. Although, not all cryptographic strategies are equal in vulnerability. Z-Text's underlying architecture, built on Zcash's Sapling protocol as well as the zk/SNARKs offers inherent security features that can withstand quantum encryption in ways traditional encryption methods cannot. The main issue is what is revealed and what remains covered. With Z-Text, you can ensure that your public keys will not be revealed to Blockchain, Z-Text secures something for quantum computers in order to sabotage. Your old conversations, identity and wallet remain safe, not through the complexity of it all, but rather by their mathematical invisibility.
1. The Fundamental Vulnerability: Detected Public Keys
To fully understand why ZText is quantum-resistant, it is important to realize why many systems not. For normal blockchain transactions, your public key is exposed each time you pay for funds. The quantum computer will take the exposed public keys and through Shor's algorithm get your private number. Z-Text's shielded transaction, using two-addresses that never disclose to the public key. The zk SNARK is proof that you've got this key without having to reveal it. The public key is inaccessible, giving the quantum computer nothing to attack.
2. Zero-Knowledge Proofs, also known as information minimalism
zk-SNARKs are inherently quantum-resistant because they have to rely on the rigor of issues that cannot be much solvable by quantum algorithms such as factoring or discrete logarithms. However, the proof itself is completely devoid of information about the witness (your private secret key). Even if a quantum machine could possibly break the proof's underlying assumptions, it's not going to have anything to go on. The proof is an unreliable cryptographic proof that is able to verify a statement, but not containing its substance.
3. Shielded addresses (z-addresses) in the form of obfuscated existence
A z-address in the Zcash protocol (used by Z-Text) cannot be published as a blockchain entry in a manner that links it to a transaction. If you are able to receive money or messages from Z-Text, the blockchain keeps track of the shielded pool transaction occurred. Your unique address is hidden within the merkle tree notes. Quantum computers scanning the blockchain can only see trees and proofs, not leaves or keys. Your address exists cryptographically however not in the sense of observation, making it unreadable to retroactive analysis.
4. "Harvest Now Decrypt Later "Harvest Now, decrypt Later" Defense
The greatest quantum threat today has nothing to do with active threats that is passively collected. Criminals can steal encrypted information via the internet, and save it while waiting for quantum computers to become mature. With Z-Text the adversary could scan the blockchain to collect every shielded transaction. However, without viewing keys and not having access to the public keys, they have zero information to decrypt. Their data is composed of zero-knowledge evidence created by design comprise no encrypted messages that will later be able to decrypt. The message is not encrypted inside the proof. Instead, the evidence is merely the message.
5. Keys and the Importance of Using One-Time of Keys
Many cryptographic systems allow using a key over and over again creates visible data that can be analysed. Z-Text, built on the BitcoinZ blockchain's implementation of Sapling allows the making use of several different addresses. Each transaction can utilize a new, unlinkable address created from the same seed. It means that even the integrity of one account is breached (by quantum means), the others remain as secure. Quantum immunity is enhanced due to rotating the key continuously, making it difficult to determine the significance for any one key cracked.
6. Post-Quantum Assumptions In zk-SNARKs
Modern zk-SNARKs often rely on equations of curves on elliptic lines, which could be susceptible to quantum computer. However, the specific construction used by Zcash, Z-Text is able to be migrated. The protocol is built for eventual support of post-quantum secure zk-SNARKs. Since the keys can never be disclosed, the transition to a completely new proving technology can be achieved by addressing the protocol and not needing users to divulge their background. The shielded-pool architecture is capable of being forward-compatible with quantum resistant cryptography.
7. Wallet Seeds and the BIP-39 Standard
The seed of your wallet (the 24 words) cannot be hacked similarly. The seed itself is simply a high-frequency random number. Quantum computers are not significantly stronger at brute force-forcing 256 bit random numbers compared to classical computers due to Grover's algorithm limitations. A vulnerability lies in determination of public-keys from that seed. Through keeping these keys secret by using zk-SNARKs seed is safe even in a postquantum world.
8. Quantum-Decrypted Metadata vs. Shielded Metadata
If quantum computers ultimately compromise some encryption aspects However, they have the problem that Z-Text hides metadata in the protocol. If a quantum machine is able to be able to tell you that an exchange was conducted between two parties, if they had their public keys. In the event that those keys weren't released, and the transaction is only a zero-knowledge evidence that doesn't have addressing information in it, the quantum computer is able to only determine that "something occurred in the shielded pool." The social graphs, the timing and the frequency are not visible.
9. The Merkle Tree as a Time Capsule
Z-Text records messages on the merkle tree on blockchains that contains encrypted notes. The structure is innately resistant to quantum decryption since in order to locate a particular note there must be a clear understanding of the note's pledge and the position within the tree. Without the viewing key, quantum computers can't distinguish your note from the billions of others that make up the tree. A computational task to look through the whole tree in search of specific notes is very big, even for quantum computers. The effort is exponentially increasing at every addition of blocks.
10. Future-proofing Through Cryptographic Agility
Finally, the most important part of ZText's quantum resistance is its cryptographic agility. Because the software is based around a Blockchain protocol (BitcoinZ) which is upgraded through community consensus, Cryptographic techniques can be replaced as quantum threats develop. Users are not locked into one single algorithm indefinitely. Since their personal history is shielded and their keys are themselves stored, they're able move into new quantum-resistant patterns with no risk of revealing their previous. Its architecture makes sure that your conversations are secure not only from threats to your current system, but for tomorrow's too.